If like me you fix computers for a livin’, you may have encountered this problem: a persistent Virus on a customer’s computer that just won’t go away. Rootkits and Trojans fall into this category; conventional Windows Antiviral methods are useless against them. Apple users don’t laugh; you get viruses too as I’d revealed in my expose How to protect your Mac for Viruses, as apparently Macs can get viruses too!
These types of Malware often employ an annoying strategy of cat-and-mouse: they make your files invisible. Thus, in your frustration, you think you’ve lost your files so you scrub your Hard-Drive. In case you did delete your files, just follow my article How to recover Data from your Damaged Thumb Drive or ZIP Archive on Data Recovery and you can get back all of your Data!
Worse, the Virus replicates like sex-crazed Rats. Lying often duplicates in multiple folders hidden from view, Rootkits and Trojans reinstall themselves on every mounted Hard-drive and re-infecting your computer every time you reboot, giving everyone else a sample of what you got, 50 Cents Candy Shop Style.
To this end, I did an article on how to remove such a Virus using a Bootable version of Fedora Linux as explained in How to recover a files made invisible by malware using Fedora and Command. You can also use Ubuntu Linux or even Knoppix or Puppy Linux; the lighter the Bootable Linux you use and the more RAM (Random Access Memory) your computer or Laptop has the faster it’ll boot from your CD/DVD ROM Drive.
You can get your Bootable Linux fix from via Google, the one stop shop for all your search needs or us my handy link list:
Bootable Rescue Disc – Scramble the F-115 Jets before dropping the Nuclear Bomb
But what if you don’t have the means to burn yourself a copy of Linux or you just can’t bother (yu lazy eeh) or you don’t like Linux, for some strange reason? I can and I have to Burn copies of Linux…..after all, that’s how I make my #BreadandButter via Virus Cleaning and Fixing computers.
However, using Linux to kill viruses, a task it wasn’t really intended for, is very difficult and requires that you know where to look in order to manually delete the *.exe, *.com or *.VBS Scripts that these viruses often manifest themselves as and under the Linux OS are laid out bare.
If it’s a VERY Large Hard-drive, deleting them manually can take hours….so get out a bag of Excelsior Cinnamon Crackers and some Jam to pass the time while you do this.
If you only have Antivirus software such as Avira Antivir as described in Kemory’s article Avira Antivir: Virus and Malware Protection, or my fave, AVAST Antivirus, you can still fix your computer by making a Bootable Rescue Disk. Using a Bootable Rescue Disc is especially useful if they block access to the Desktop and Files and you’re not particularly proficient at using DOS (Disk Operating System) Command Line in Safe mode, my other favourite tool to use when fixing computers.
It’s also useful if you’re not able to get to the Desktop and even set the Antivirus program to do a Boot Scan. You can actually do so without the Desktop via Command Line if you know how to use MS-DOS and locate the program files for the Antivirus and set it to do a BootScan. Rootkits and Trojans reinstall themselves via regeneration from hidden copies during boot.
Hence the reason why using Linux is an effective way of dealing with them, as by booting with Linux, you eliminate Windows out of the equation and stop them from re-loading into the system.
The ABSOLUTE last line of Defense against such viruses is nuking your Operating System via backing it up and reinstalling the OS via a Bootable Disc, a trick by the way that’s known to make your computer run faster as noted in Tips and Tricks on how to make your computer run faster.
So before you back out a Bootable copy of Microsoft Windows XP or Windows 7 and go nuclear on your computer, you can make a Bootable Rescue Disc.
How to make a Bootable Rescue Disc – AVAST to the Rescue the Damsel in Distress
The Steps to making a Bootable Rescue Disc are fairly simple using my fave Antivirus programme, AVAST Antivirus, my fave mainly because it talks in a woman’s voice and does fairly thorough and fast Boot Scans. This time I’ll Do it in Pictures, as y’all seem to love it that way!
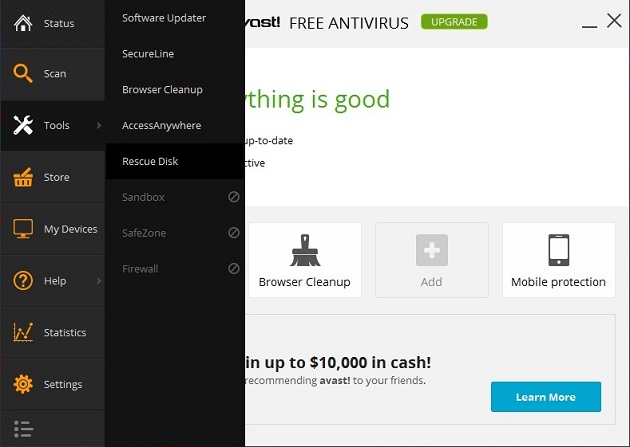
Access AVAST Antivirus from your Desktop and Go to Tools and Select Rescue Disc as shown below
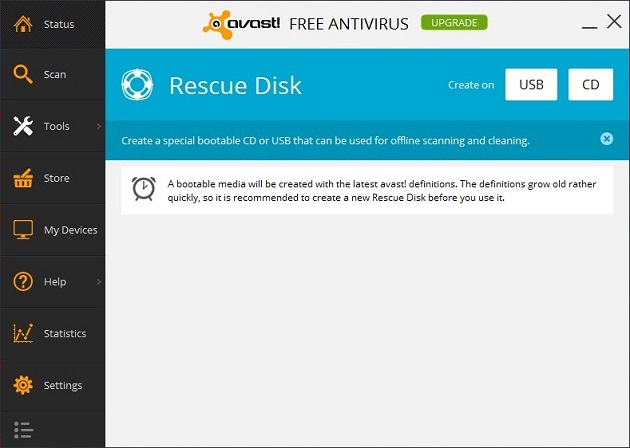
Select what for you want your Bootable Rescue Disc to take, be t on a USB Thumb Drive or CD. If it’s a USB Thumb Drive, you have to makes sure to use an empty formatted Thumb Drive
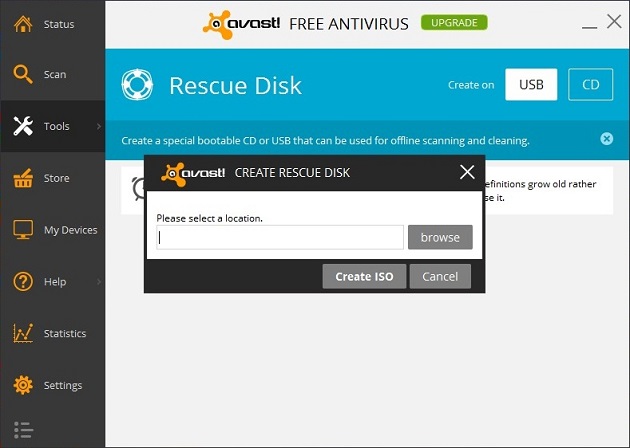
Select CD. A pop-up box appears and prompts you to save the *.ISO file to a location on your computer
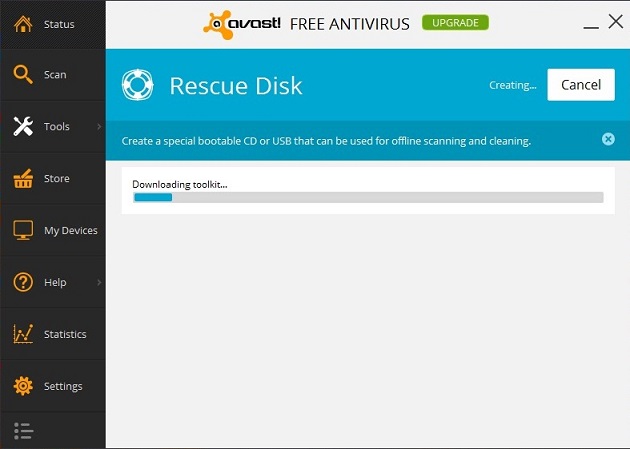
Then wait. It’ll take quite awhile as AVAST Builds the Bootable Rescue disc via downloading the latest Virus Definitions from their Antivirus Server.
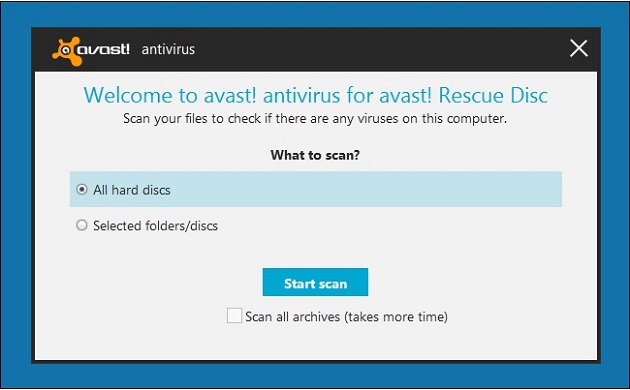
To use your Bootable AVAST Rescue Disc is fairly simple; just pop it into the CD/DVD ROM Drive and set the Boot Preference to the CD/DVD ROM Drive to boot from the CD that the Disc is burned unto as shown below.
Be warned though; AVAST take quite awhile to gather itself and make the disc! If like me you’re pressed for time and need a Bootable Antivirus Rescue Disc and you’re NOT picky, then Google “Softpedia.com Rescue disc” and get a decent list of free Antivirus Bootable Rescue Discs ranked by popularity of usage…which means they’re good and they change from time to time, hence the reason why I’m NOT listing them here.
If you’re really into this System Admin thing like some peeps I know, they you’ll be wanting other tools aside from Antivirus software that can boot. Here’s a list of Bootable Rescue Discs that are a Sys Admin’s Swiss Army Knife:
That’s it dear reader! Bootable Rescue Discs either made using a Linux Distribution, downloaded from an Antivirus program or made by a third party Developer are a Sys Admin’s Swiss Army Knife to Rescue the Damsel in Distress in your workplace.
